DEW #153 - New IPv8 Draft, macOS Threat Detection LLM Evals & Canaries in your CI/CD Pipeline
Never ask the IETF about odd numbers in versioning
Welcome to Issue #153 of Detection Engineering Weekly!
✍️ Musings from the life of Zack:
I’m spending time in the Caribbean this week with my family and wish I could write this newsletter everyday with nice weather and an ocean nearby. Luckily New England does have the Atlantic, but it’s not the same for two reasons. First, the fruit is so much tastier down here. Lastly, I can’t find an Oscar the Grouch with dance moves quite like this Oscar :D
I’m hosting a webinar with Allie Mellen from Forrester on April 30th where we’ll be diving deep on security operations and how AI is working and not working for all of us. We’ve had awesome discussions around this in the past. Feel free to register and come roast me in the chat
Sponsor: Push Security
Register for a brand new research-focused webinar series from Push Security
The browser is the place where modern breaches happen, powered by a huge amount of attacker innovation — countless ClickFix variants, new malvertised phishing campaigns, and device code phishing attacks being powered by brand new PhaaS kits and AI tools. And we’re only in April.
Join Push Security threat researchers, along with incredible guests like John Hammond, Troy Hunt, and Matt Johansen, in a brand new webinar series deep-diving into the State of Browser Attacks.
💎 Detection Engineering Gem 💎
Internet Protocol Version 8 (IPv8) by Jamie Thain
Ok, here’s a confession, but it’s more of a brag than something to be embarrassed about. When I went to college, I studied networking and network security extensively, as the 2008-2012 era had a strong focus on it. A lot of what my classes entailed was setting up large VM farms and networking devices on server racks. I lucked out because I got really good at networking, and part of that involved studying RFCs. I love RFCs. My favorite RFC is 1034, DNS, the coolest protocol in the modern Internet.
My co-worker sent out a link this week amid the Opus-4.7 news about the IETF skipping odd-numbered Internet Protocol RFCs and moving directly to IPv8. This specific proposal (not yet accepted) attempts to address the fragmentation of IPv4 & IPV6 networks around IP address assignment, DNS, NTP, telemetry, authentication, route validation, and access controls.
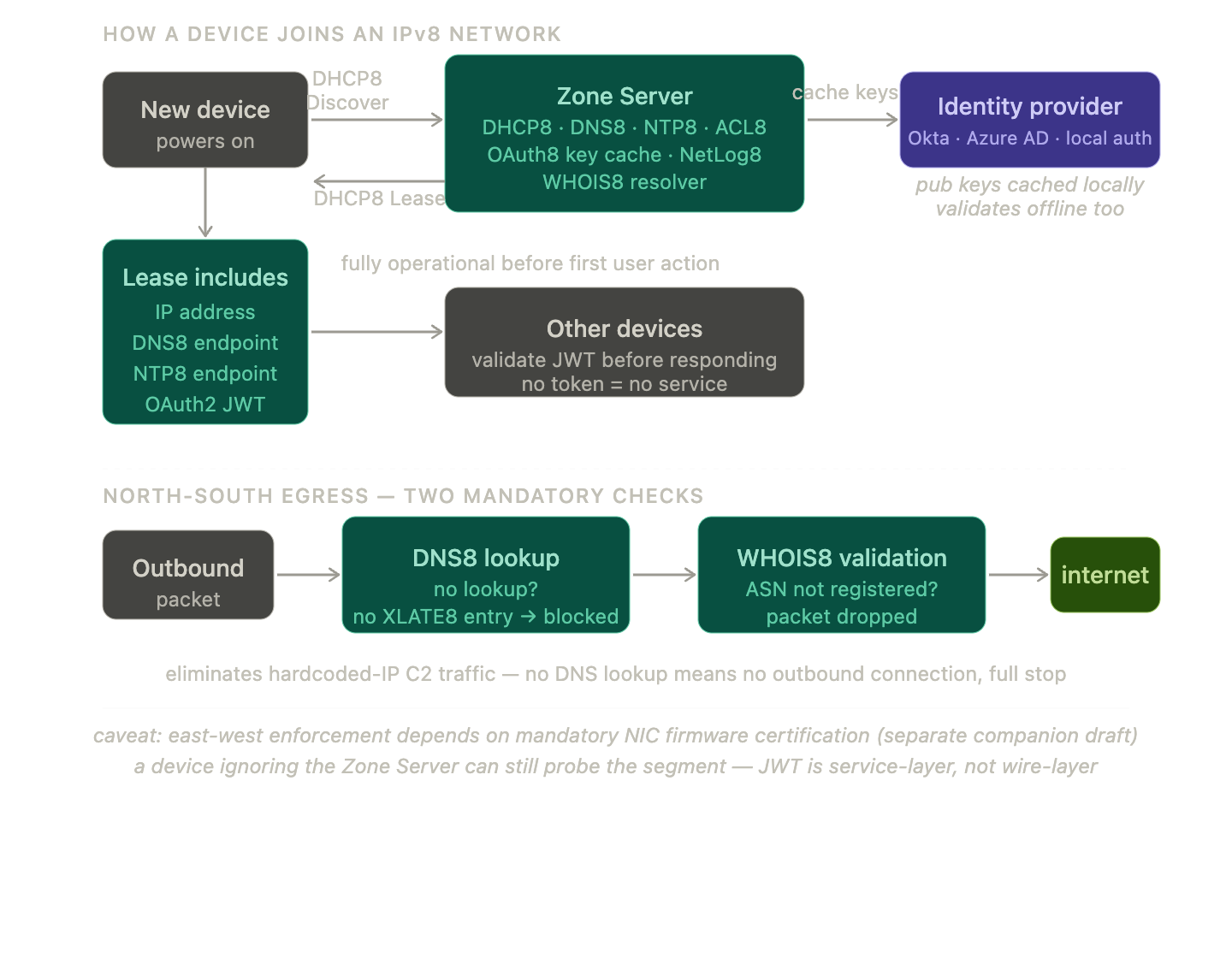
Jamie Thain, the proposal’s author, suggests that these fragmented services can be reconciled through a singular concept called a Zone Server. This Zone Server assigns DHCP leases that contain network information for everything I listed above. As Thain puts it:
A device connecting to an IPv8 network sends one DHCP8 Discover and receives one response containing every service endpoint it requires. No subsequent manual configuration is needed for any service. The device is fully operational -- authenticated, logged, time-synchronised, zone-policy-enforced -- before its first user interaction.
The most interesting part of this proposal, IMHO, is the authorization model. Every manageable element in an IPv8 network is authorized via OAuth2 JWT tokens. Like what Thain said in the quote, when a new device joins, it sends a single DHCP8 Discover and receives a lease containing the device’s configuration, including a JWT. The “OAuth2 Authority” can be hosted on a home router or on an external IdP such as Google Workspace, Okta, or Azure AD. The Zone Server stores the public keys for these authorizations, so local devices can verify token validity with the Zone Server before interaction. It reminds me a lot of Tailscale, but unlike Tailnets, rogue devices can still join your network; you just need to make sure peer devices validate tokens before they talk to it.
The second most interesting thing is DNS. Every outbound connection must have a valid DNS8 lookup before it traverses the broadcast domain; otherwise, it is automatically blocked. This helps protect against malware infections calling back to a C2 server.
As Claude pointed out, this authorization layer exists at a higher layer in the OSI stack. Attacks can still occur on lower layers. Putting my networking nerddom aside, it’s refreshing seeing how Internet-scale engineers are thinking about solving issues around security and having solutions being a feature of the protocol itself. This prevents service fragmentation, poor visibility, and the need to stitch together different security layers and hope they work.
🔬 State of the Art
This was a fun episode of Discarded where the hosts interviewed their coworker, Stuart Del Caliz, who’s a threat detection engineer at Proofpoint. When I think of writing rules and detections, my mind usually drifts towards researching and deploying log-based detections in a SIEM. Del Caliz, on the other hand, focuses on Suricata & YARA rules for malware using appliance products via the Emerging Threats Ruleset. The team has a robust malware sandbox that enables Del Caliz and the detection team to identify patterns in C2 traffic and binaries and to generate alerting and blocking mechanisms for customers.
Luckily, the Emerging Threats Ruleset is available for download, so you can set up your own Suricata lab to test it out.
macOS Threat Investigation Benchmark by Cotool Research
Friends of the newsletter Cotool published their latest research benchmark on the efficacy of the latest foundational model around macOS investigations. What makes this interesting is that, unlike CTF events, which have a clear incremental path to success, this benchmark uses logs and telemetry from an Odyssey stealer infection. The agents were given access to 14 log sources across hundreds of thousands of events and had question harnesses across 36 tasks in incident response, threat hunting, and detection engineering.
GPT-* models performed very well across Accuracy, Speed, and Reliability, and were middle-of-the-pack in cost. I think the most interesting finding here is that Cotool rewarded models based on task difficulty. For example, Incident Response was the hardest and most expensive among the tracks, and GPT-5.4 and 5.3 Codex had the best combination of accuracy and cost efficiency. Opus 4.6 had the same accuracy but cost nearly double that of GPT-5.4
Detecting CI/CD Supply Chain Attacks with Canary Credentials by Alessandro Brucato
The Tracebit team just released a clever canary detection mechanism for supply-chain attacks against GitHub Actions, similar to what we saw with the TeamPCP campaign a few weeks ago. Security teams can pull in their community edition GitHub action, which generates per-run canary credentials, such as AWS tokens. If your security controls fail or you fail to detect an attack, you can use these tokens as a reliable alerting tool that points to the repo and specific GitHub action.
They have a community edition, which is always great to see, because you can sign up and try it without all the vendor marketing gates and FUD that is commonly shoved down security people’s throats :).
Codex Security by OpenAI
The foundational labs are leaning more and more into cybersecurity use cases. With Mythos’ release last week, OpenAI released a Codex Security preview that allows vetted cybersecurity professionals to use an advanced version of Codex to scan their repositories for vulnerabilities. The “vetted” part of this announcement is interesting because Mythos was heavily gated in their announcement, whereas OpenAI has made it easier for folks to apply and get access if they meet certain verification criteria.
Sponsor: Spectrum Security
Stop the Grind and Kill the Detection Backlog with Spectrum
You know the grind: Research the gap. Understand the environment. Write the logic. Tune it. Deploy it. Watch it break when something upstream changes. Repeat. Backlog never shrinks.
Spectrum is now available. One platform that continuously maps your coverage, authors deployment-ready detections tailored to your stack, and keeps them resilient, so your expertise drives strategy, not maintenance.
☣️ Threat Landscape
Two U.S. Nationals Sentenced for Facilitating Fraudulent Remote Information Technology Worker Scheme that Generated $5M in Revenue for the Democratic People’s Republic of Korea by U.S. Department of Justice
Why is it always someone from New Jersey?
Kidding, unless you are a Jets fan. The DoJ released a sentence announcement for two U.S. nationals who became facilitators for Wagemole over several years. According to the announcement, they helped generate over $5 million USD of revenue for DPRK, stole identities of close to 100 U.S. persons, and worked at 100s of U.S. companies.
I post a lot about the DPRK in this newsletter because it hits so close to home, given that I work in tech. I also post a lot about DPRK in this newsletter because I have to follow up with these Wagemole stories by watching this Key & Peele sketch:
NIST Updates NVD Operations to Address Record CVE Growth by NIST
NIST released updated guidelines on how they will perform CVE enrichment moving forward. They’ve had nearly two years of turmoil trying to keep up with enriching CVEs for their National Vulnerability Database. I think this failure to enrich every CVE is due to two things: funding shortages and AI. I’ve linked a ton of stories here from open-source maintainers like Daniel Stenberg, saying that AI is creating too much vulnerability research slop. But I do believe recent CVEs have been at least AI-assisted, which helps increase velocity.
In their announcement, NIST says it will prioritize CVEs into three categories: CISA KEV entries, vulnerabilities in software used by the federal government, and CVEs for Critical Software, as detailed in an executive order from 2021.
There are other playbook changes regarding severity scores and modified CVEs, but IMHO, the significant reduction in CVE enrichment is the big news here. I hope we can find a way, as a community, to fund efforts to enrich CVEs in lieu of the NVD.
MCP Supply Chain Advisory: RCE Vulnerabilities Across the AI Ecosystem by Moshe Siman Tov Bustan, Mustafa Naamnih & Nir Zadok
The Ox Security Research Team found four attack surfaces in Anthropic’s MCP Protocol implementation. These attack surfaces led the research team to disclose vulnerabilities to dozens of open-source repositories and get to 10 CVEs and counting. The way it works is how this software sets up MCP servers and what they allow as input into their configurations. The command injection is via exposed tools that can add an MCP configuration. When you add an stdio transport, you can specify an arbitrary bash command that allows remote code execution.
The team disclosed this vulnerability to Anthropic but the protocol specifically allows this option and is by design. The problem here is when users of these MCP-enabled projects don’t know about the insecure configuration and deploy it to the Internet allowing the remote code execution. There are situations where this RCE can be unauthenticated or authenticated, but for the most part, it points out that anytime you allow arbitrary configurations to be uploaded by users, you risk exposing yourselves to attacks like this.
Understanding security warnings when opening Remote Desktop (RDP) files by Microsoft
Microsoft finally released security updates to help warn users of malicious RDP files before they become victims of an infection or social engineering attack. Attackers leverage RDP files to initiate remote connections to victim computers, often using them to steal files, take pictures or steal contents of your clipboard. Now, users of the latest security update will get warnings when double-clicking on these files, hopefully preventing some of these infections from happening.
With the advent of ClickFix, my hopes aren’t too high, but sometimes security is about incremental steps versus massive swings.
🔗 Open Source
Magika is file on steroids. It uses a deep-learning model under the hood that helps classify files with what they claim is 99% accuracy. It was trained on 100 million+ samples and 200+ content types. The cool part here is that this is the model and tool used by Google to help detect filetypes on Gmail, Drive and Safe Browsing. I imagine they can use this to route files based on their content types to different internal security services for scanning.
Locally ran MCP server that helps researchers and defenders connect to 27 (!) security tools for CVE lookup and enrichment. Unfortunately you won’t get much data anymore from NVD, but it has some great integrations with ATT&CK, internet scanners and even VirusTotal.
Cyber Neo is a Vulnerability research plugin for Claude Code. It has 11 security domains it tries to scan for, and each domain has toolsets and markdown instructions for Claude to execute to render findings.
GoLang credential and secrets harvesting tool that uses eBPF to skim credentials off from syscall events. It’s like a Linux rootkit that only cares about secrets. It has some interesting capabilities, such as memory-only execution and anti-detection capabilities. It tries to intercept secrets across SSH, PAM, the command line and does some file-based discovery for things like API keys and cloud secrets.
xnew is a low-footprint and fast file appender. It is contextually aware of every line inside the file, and it will only append unique lines not already present. This has always been a pain for me everytime I’ve had to cat x | uniq | sort | uniq , which can sometimes take forever when the file is super large.