DEW #150 - macOS Endpoint Security Firewall, EDR telemetry updates & Supply Chain Bonanza
pls no more OSS compromises
Welcome to Issue #150 of Detection Engineering Weekly!
✍️ Musings from the life of Zack:
We completed a 5-hour back-and-forth car ride over the weekend with mostly chill kids, no car sickness, and even some napping. It doesn’t seem like much but it made the trip wayyy less stressful.
I skipped last week to take some time off after RSA. Thank you to everyone who came up and said hello to me, as well as to those who hung out at the Detection & Response Happy Hour!
I finally set up Claude to be an “executive assistant”. It’s been helpful to have it sift through email, Slack, and Calendars and give me the most important things up front. It did take some prompt tuning to separate what matters from what is noise, but I recommend setting this up for people who have a busy personal or work life.
Sponsor: Permiso Security
Every identity. Every environment. Know static posture and runtime behavior.
Attackers aren’t breaking in anymore. They’re logging in. And they’re not just targeting human accounts. Service accounts, OAuth tokens, and AI agents are just as exposed and far less monitored. Most detection tools weren’t built for that reality. Permiso was, which is why we won the 2026 SC Award for Best Threat Detection Technology. See how it works in our product tour.
💎 Detection Engineering Gem 💎
Building a Firewall ...via Endpoint Security!? by Patrick Wardle
<rant>
Apple and lack of accessibility to secure telemetry: name a better duo. Jokes aside, I have such a love-hate relationship with Apple products. I use them for everything. The ecosystem is SO good. I can’t imagine not working on a MacBook, surfing the Internet, taking calls on an iPhone, or sporting around my AirPods Max. They integrate their technologies so well and make them easy to use across devices, and if my parents can figure out how to use them (sorry, Dad & my in-laws), then you know they do something right.
What infuriates me is how opaque they choose to make their devices to researchers, security tinkerers, and security teams at companies who pay Apple a lot of money. There are myriad nation-state threat actor cases in which a sophisticated exploit runs against an Apple device, and victims are unaware of what happened. In every case above, detection required either an external forensics lab (Citizen Lab, Amnesty Tech), corporate network monitoring catching anomalous traffic (Kaspersky), or a specialized third-party iOS monitoring tool (iVerify). Apple’s own platform produced no victim-facing signal.
</rant>
Luckily, we have the macOS researcher community, and Patrick Wardle is one of the lead researchers in this cause. Wardle routinely reverse-engineers macOS releases to discover new capabilities and features to share with the wider community. In this latest macOS 26.4 release, Apple’s built-in Endpoint Security product got some updates. This didn’t come with much (any) documentation, so Wardle built a harness to explore new data types within the framework and determine how to implement them. There were six new event types added with unhelpful names, such as ES_EVENT_TYPE_RESERVED_1
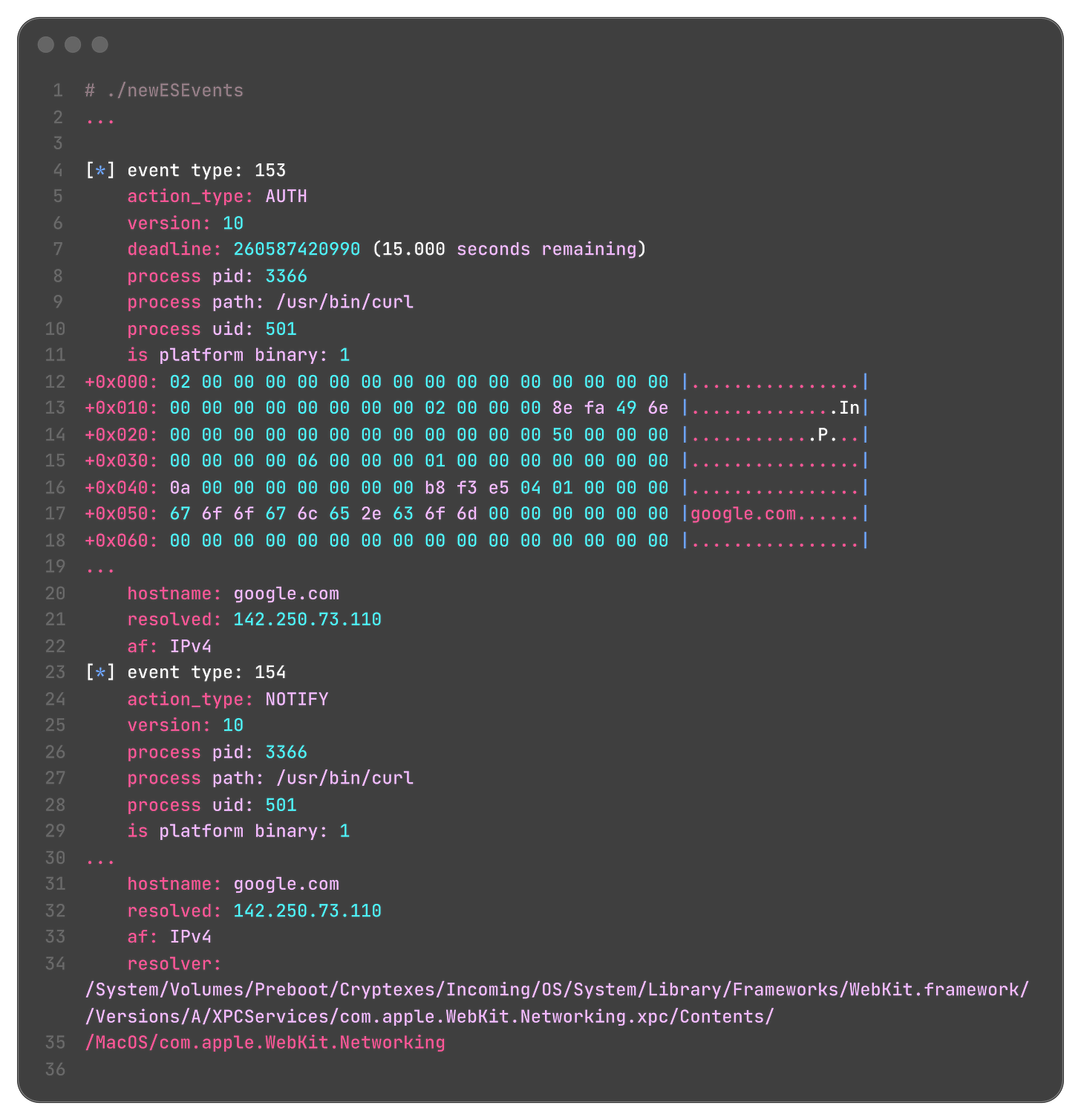
So, Wardle built a harness to subscribe to the Endpoint Security event stream and filter out the event types listed above. He sucessfully subscribed to 3-6, and had such a clever way to print the raw bytes from these subscribed events into essentially what is a hex dump. Instead of parsing each byte, he fed his methodology (plus the dumps) into Claude Code, and it found out they were network logs:
One thing I learned from Wardle is that these event logs send two events to a subscription: an AUTH and a NOTIFY event. The AUTH allows you to allow or deny the event. So, in this case, imagine cURLing a suspicious domain from a ClickFix attack and your Endpoint Security event software denies it. The NOTIFY event is for logging and might be useful for on-device correlated alerts in an EDR or for sending it to your SIEM.
I am really starting to enjoy the macOS detection & response capabilities coming out, and I am hopeful that the research from the small, tight-knit macOS security community can bring them to the masses.
🔬 State of the Art
The C2 Trap by James Rowell
Shiny object syndrome is a phenomenon I see a lot in security, and it can dangerously bias your work towards what is new and trendy. A classic example of this is a security operations team reading threat intel reports on nation-state activity and trying to write rules to catch the latest TTPs. What they may not realize, for example, is that this nation-state targets technologies that the team rarely uses, or they don’t fit into the threat actor’s target set due to their size or industry. We love our shiny objects!
In this post, Rowell describes how detection engineers can fall victim to this syndrome by targeting the wrong parts of the MITRE ATT&CK chain. One of my favorite quotes they use here:
The first mistake that teams make is to treat C2 and exfiltration as if they are specific behaviours. They are not. They are outcomes.
This is super concise for a number of reasons that Rowell points out. First, the “outcomes” portion of this quote means you can’t stop exfiltration without understanding the underlying behaviors. It begs the question: when an actor successfully exfiltrates data from your environment, how did they do it? Was it uploading to a cloud service, a good old-fashioned SSH session, or perhaps emailing a large zip file to their inboxes?
Rowell challenges readers to move to the left of exfiltration if you have to start somewhere. A lot of things have to go right for the attacker in order to get to this stage. So, focusing on behavior chokepoints in persistence, privilege escalation, and lateral movement can meaningfully reduce the complexity of your rule backlog. It’s also likely that you have a limited set of attack paths for data exfiltration, whereas there are many ways to exfiltrate data, as I stated above.
Detection via Deception — Using your SIEM as a Free Deception Platform by Regan Carey
Honeytokens are widely regarded as a low-cost, effective detection tool for identifying threat actors targeting your environment. Thinkst Canary is the prime example of a company that creates this technology, and you can use their canaries for free across a variety of technologies. In fact, it’s a great learning experience for those building detection labs or securing their home networks to deploy these and watch threat actors try to use them, especially if you intentionally expose them.
In this post, Carey does a great job of framing some of the issues people have with deploying canarytokens and calls out some misconceptions behind deception-based alerting and honeytokens. First, the technological barrier to using honeytokens isn’t low, so you just have to find a way to deploy them and send any corresponding alerts. Second, people may believe that their environment isn’t complex enough to warrant using honeytokens, when in fact they may be better for small organizations and environments due to the cost of entry for security products.
They round out the post with an example of using MITRE Engage to deploy and monitor honeytokens leveraging native Azure, Sentinel, and KQL functionality.
macOS EDR Telemetry: A Structured Framework for Evaluating Endpoint Visibility by Kostas Tsialemis
I first covered Kostas’ EDR Telemetry Project in October 2024, and it’s grown so much since then! The project provides a framework for benchmarking the detection & response capabilities of various EDR vendors across Linux and Windows. With this release, the team added a macOS benchmark. The framework comprises 16 categories and 58 subcategories across 8 EDR projects.
I’m glad to see them tackle macOS: infostealers have been a popular target for cybercriminals. Apple built Endpoint Security (ES) for security vendors to subscribe to, similar to Windows ETW or eBPF on Linux. The issue with ES is it’s super noisy, and because it’s not technically an inline hook, there’s not the same level of inline blocking as you’ll see on Windows and Linux. They released a companion query-generation tool that people can run while comparing their EDRs or security tooling against the framework.
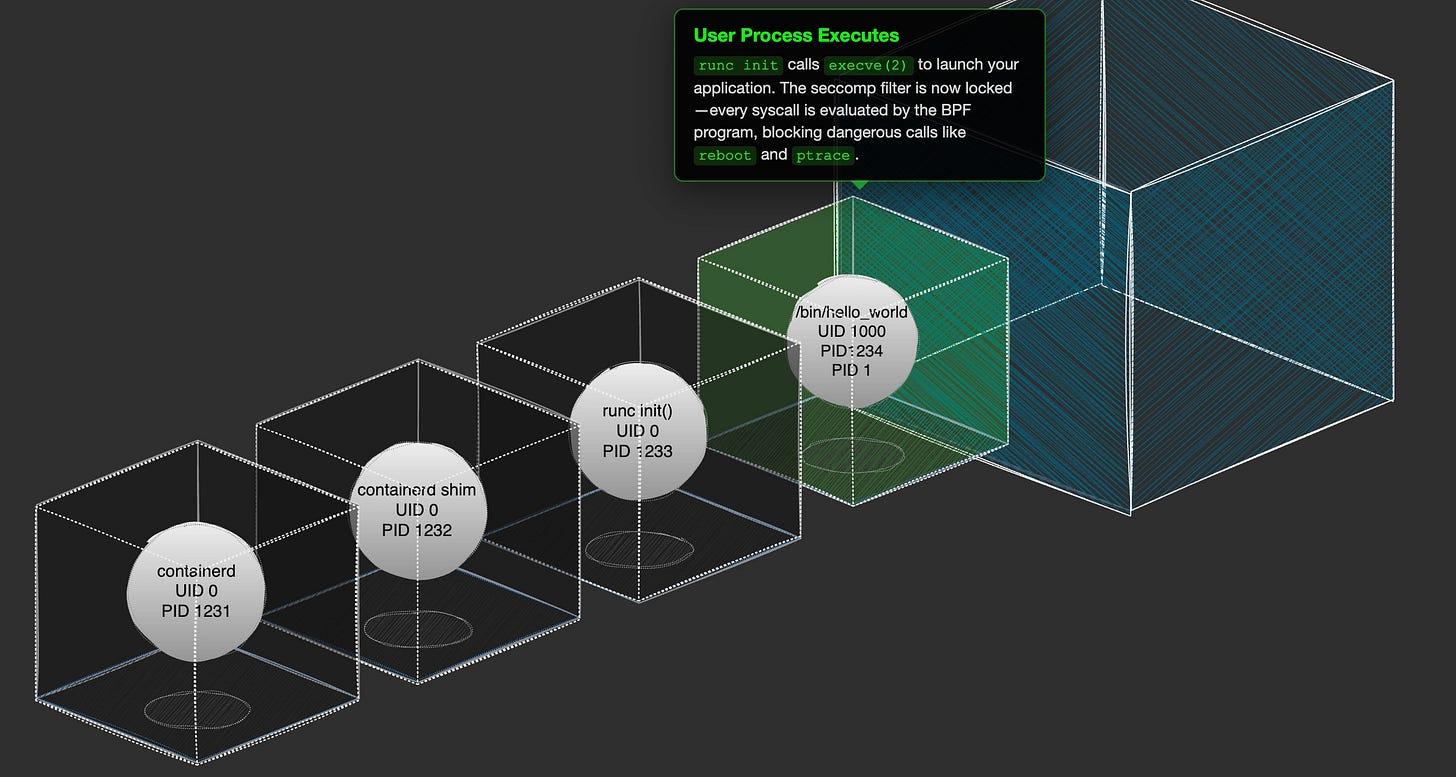
SecCompare by Mark Manning
Long time friend of the newsletter, Mark Manning, is one of the leading researchers in container and Kubernetes security. He recently gave a talk at BSidesSF that surveyed various Linux security guardrail tools and their corresponding threat models. Within the talk, he showed his tool, SecCompare, which helps people understand SeccompBPF filters, and compare and contrast expected behavior from filters you generate versus baselines. These can get tricky as there are peculiar attack paths among many different Linux syscalls that can bypass a seccomp filter without you realizing it.
He’s got a sick Linux syscall table lookup with information on each syscall as well as labels around how you can abuse them. The interactive “how do containers work” demo is sick, too.
Slightly safer vibecoding by adopting old hacker habits by Halvar Flake
Vulnerability Research GOAT Halvar Flake released a timely post on his setup for coding in the wake of all of the TeamPCP supply chain attacks over the last few weeks. It’s a short but sweet post that starts to bring up “old” ways of doing things I learned when I first started in security. A basic setup involving a rented server, SSH, and a clear separation between your physical computer and your coding machine seems secure because you don't have any personal information, keys, or crypto wallets on the rented server.
I’ve been thinking a lot about old concepts from 14-15 years ago. We have been in container nirvana for the last 8 years or so, and the security boundaries are hard to nail as you begin to develop more and more in them. You load keys inside containers, push them to remote registries, and build them alongside your code. Each step of the deployment pipeline becomes an attack vector, and people aren’t paying attention to the endpoints writing this code, which are also part of the pipeline.
I can’t wait for Vagrant to come back, as it was my favorite tool for years and years, and virtual machines are way more “secure” by default. Now it’ll just be containers inside a local VM 😂.
Sponsor: Blu Raven Academy
Threat Hunting + Detection Engineering, Powered by Advanced Analytics
Master practical threat hunting and detection engineering through hands-on training with advanced analytics, real-world scenarios, and exercises designed for defenders who want skills they can apply immediately.
☣️ Threat Landscape
Emerging Threat: The Open Source Supply Chain Ecosystem is Front and Center
I take one week off from writing this newsletter, and now the software supply chain is on fire! I am linking posts to several compromises over the last 2 weeks that fall into two buckets: Axios & Nation-State Activity and TeamPCP & Cybercriminal Activity. This is becoming more significant from a detection perspective because the expertise required to understand how threat actors carry out these attacks is becoming more prevalent in our detection & response community.
The other component to call out is that the impact of these attacks extends beyond cryptominers; they can serve as primary, secondary, and tertiary initial access vectors as the bad guys work through the exfiltrated code, secrets, and infections sourced from these compromises.
I am linking two stories from $DAYJOB, so full disclosure, they are my colleagues and excellent researchers.
Compromised axios npm package delivers cross-platform RAT by Christophe Tafani-Dereeper
The first set of news, as of me writing this (Mar 31), is that the very popular Axios library for JavaScript was compromised. Axios has over 3 million weekly downloads, and these downloads range from individual developer laptops, CI/CD systems, and production environments. The threat actor compromised the owner’s account and inserted a backdoor in the dependency list. This malware had payloads for macOS, Windows & Linux. Two versions of the compromised package were released using the NPM publishing token and were exposed for around 4 hours.
Christophe’s analysis and timeline are excellent here. He covers each payload and the second-stage RAT, and also notes that this attack didn’t necessarily work in many environments due to errors in the initial loader logic.
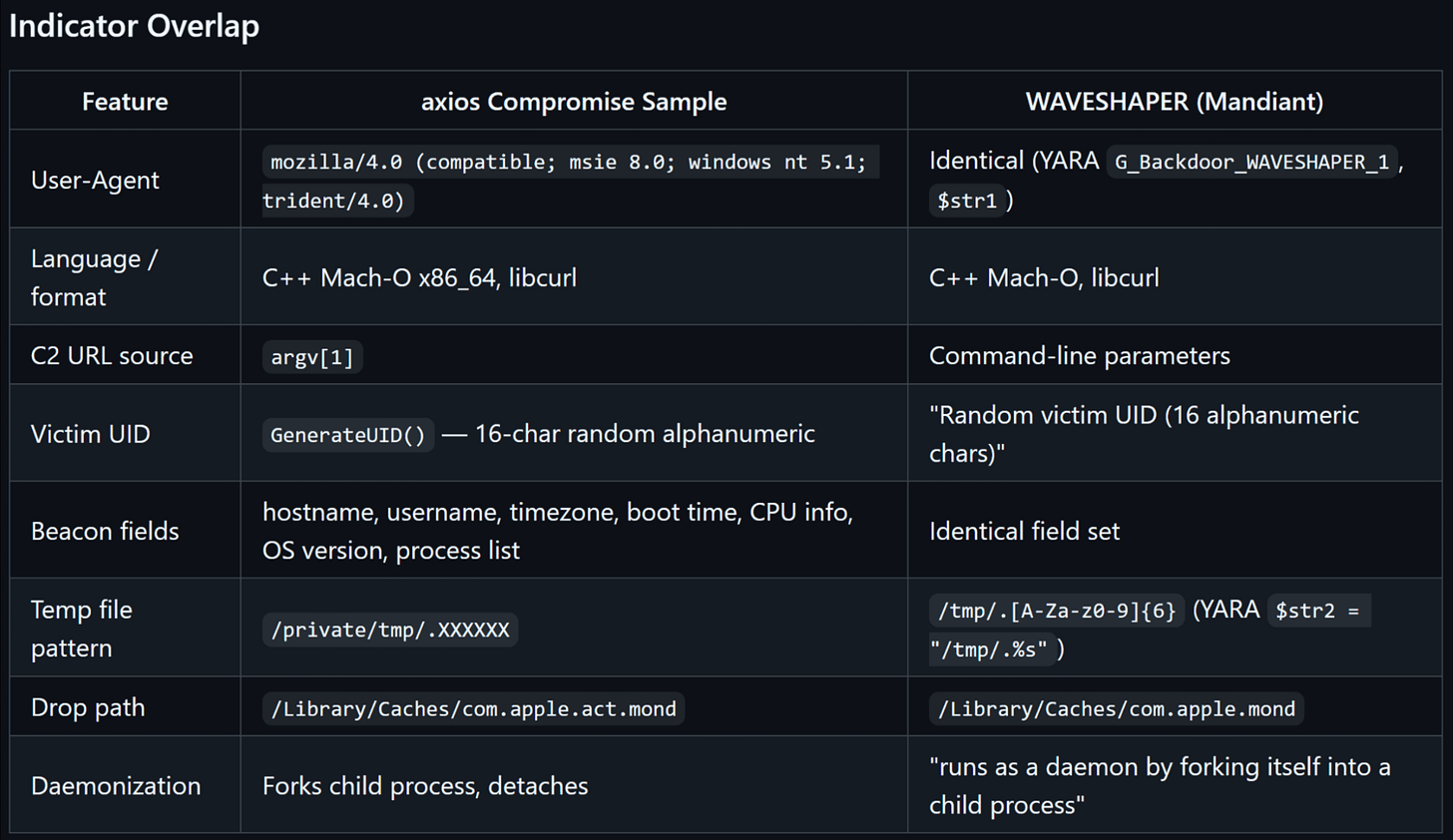
Inside the Axios supply chain compromise - one RAT to rule them all by Ruben Groenewoud, Samir Bousseaden, Salim Bitam, Joe Desimone, Colson Wilhoit & Andrew Pease
This post from the Elastic Security Research team helps shed light on the malware payloads in the second stage of the Axios attack. They said that the RAT dropped on this stage shares a “significant overlap” with WAVESHAPER, a malware family tracked by Mandiant that is connected to a DPRK-linked threat cluster. I thought this was a helpful table to show the details of this campaign compared to WAVESHAPER data:
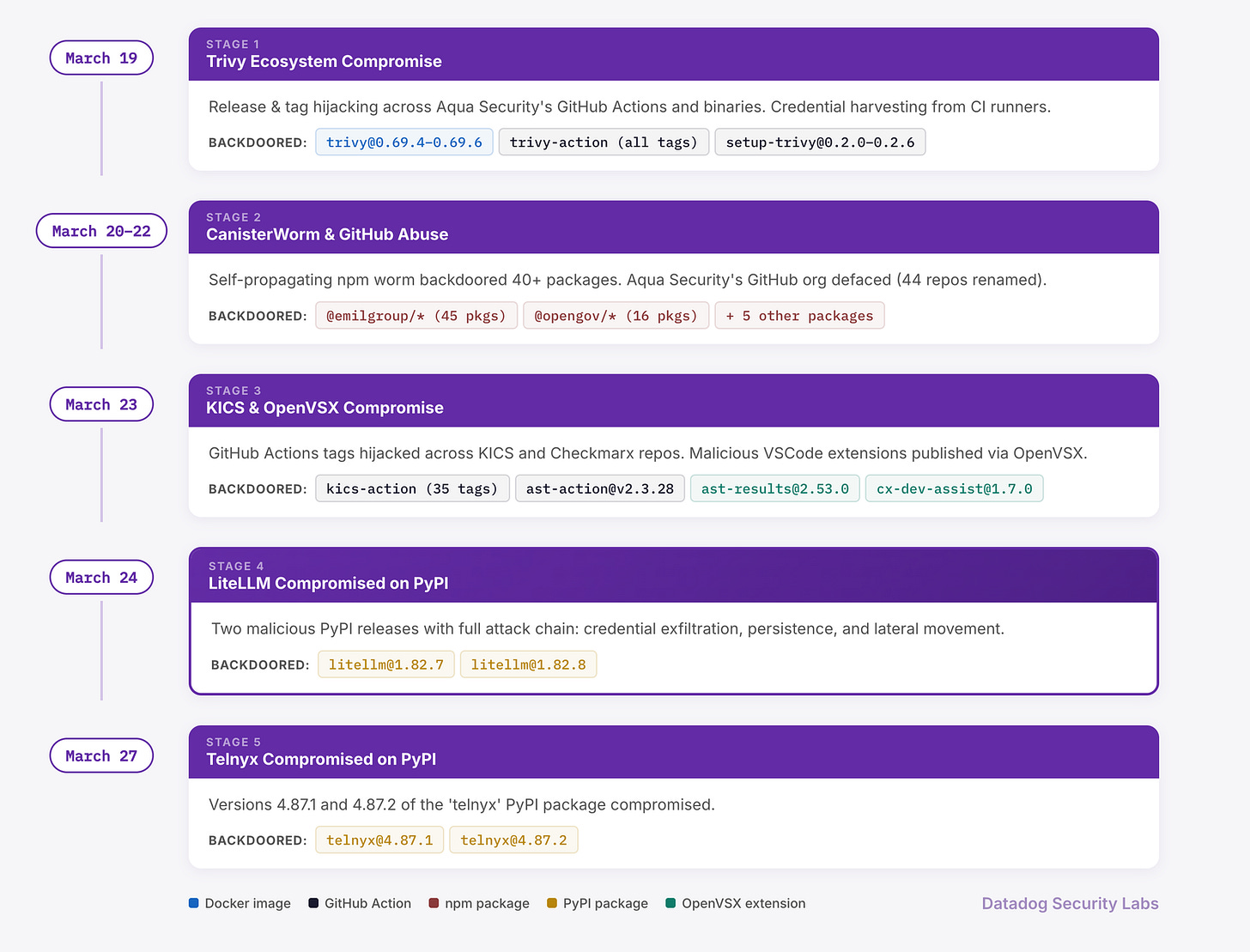
LiteLLM and Telnyx compromised on PyPI: Tracing the TeamPCP supply chain campaign by Nick Frichette, Sebastian Obregoso, Christophe Tafani-Dereeper & Emile Spir
The fallout from the Trivy compromise led to several package compromises, and LiteLLM & Telnyx were among the bigger ones.
The timeline above helps explain my take at the start of this section, a round primary, secondary, and tertiary compromises. Specifically, look at the BACKDOORED sections of each box. Given the many integration points in a CI/CD pipeline, rotating one credential doesn’t imply that another access point could provide a backdoor.
TeamPCP Supply Chain Campaign by Rami McCarthy
There has been some amazing research on this campaign by several researchers and vendors, and Rami led the way throughout. If you need a quick reference blog that’s easy to navigate, he built a beautiful website outlining the campaign so you can do just that. There are references to the timeline itself, IOCs, the payloads, unanswered questions, myths, and a nice playlist with songs for each part of the compromise!
🔗 Open Source
Sigma ruleset for detecting malicious activity within agent behavior. It’s more of a pure detection-and-alerting toolset than an EDR, compared to some of the “Agent EDRs” I’ve linked in the newsletter. It’s listing 42 different Sigma rules, which is an impressive set for agent threat activity.
OpenClaw plugin that provides an AI gateway and several governance functions to help secure your OpenClaw deployment. What’s cool is that it hooks OpenClaw to scan every skill, MCP servers, and plugins before they are installed and used by the agent. It also has some code security scanning capabilities, as well as run-time monitoring through the gateway.
awslabs/threat-modeling-mcp-server
Locally-run MCP server that provides threat modeling capabilities and tool calls. It uses the STRIDE framework to contextualize the application or code you are modeling and attempts to learn the application's business context before providing recommendations.
Yet another awesome-* repo for skills on Codex. It’s similar to the threat-modeling MCP server above, but primarily relies on skills to help shape secure-by-design coding practices and inject security tests into code artifacts.